 Your new post is loading...
 Your new post is loading...

|
Scooped by
Gust MEES
|
The solution for Smeets and his team though is not to pile on extra layers of authentication, but rather to distribute them. And that's where blockchain comes it. Because the blockchain functions via a distributed and encrypted ledger shared across all of a network's users and devices, it creates a network of authentication that is verifiable and not easily hacked. With blockchain implemented, a device cannot access a network unless it is verified through the entire ledger. In this scenario attacks like Mirai become significantly more difficult, if not impossible, because a hacker would need to modify the entire ledger, and not just the credentials of any one device.
Ericcson Research demonstrated a proof-of-concept of this idea at the 2017 Mobile World Congress in Barcelona this past March. The researchers set up a small WiFi network that used blockchain authentication instead of a typical username/password setup. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/21st-century-learning-and-teaching/?&tag=blockchain

|
Scooped by
Gust MEES
|
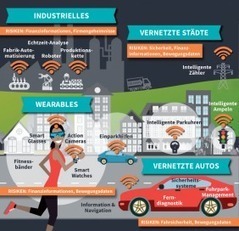
Der Begriff „Internet der Dinge“ ist bereits Ende des vorigen Jahrhunderts zum ersten Mal gefallen. Heute treibt das IoT (Internet of Things) nahezu alle Branchen und Industriezweige um. Wer mit der Digitalisierung nicht Schritt hält, hat wenig Chancen auch in Zukunft zu bestehen – davon sind inzwischen fast alle Vertreter führender Industrie-Unternehmen in Europa überzeugt. Doch in jeder Branche gibt es spezielle Herausforderungen, wie die digitale Transformation am besten umgesetzt werden kann. In Berlin kamen in dieser Woche über 1.000 Vertreter führender Industrie-Unternehmen in Europa zusammen, um auf der „Industry of Things World“ über die aktuellen Herausforderungen zu diskutierten. Learn more / En savoir plus / Mehr erfahren: http://www.scoop.it/t/21st-century-learning-and-teaching/?&tag=Internet+of+Things http://www.scoop.it/t/21st-century-learning-and-teaching/?&tag=Digital+transformation

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|
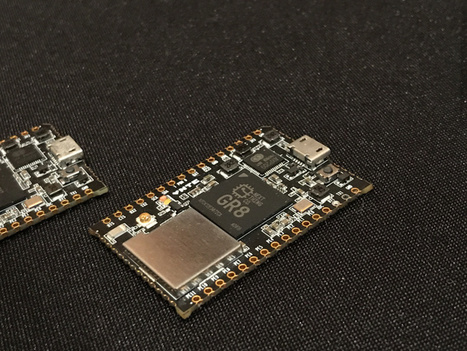
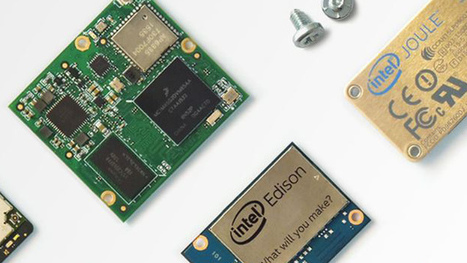
Say you want to create the next generation of voice recognition-enabled, AI-ensmartened, buzzword-laden gadget. The fist thing you need to do is pick a platform. Arduino isn’t powerful enough. The Raspberry Pi works great for prototyping, but going from Pi to production is a many-step process. Next Thing‘s Chip Pro is stepping up to fill the gap with a smart development kit for IoT creators. Learn more / En savoir plus / Mehr erfahren: http://www.scoop.it/t/21st-century-learning-and-teaching/?tag=Internet+of+Things

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|
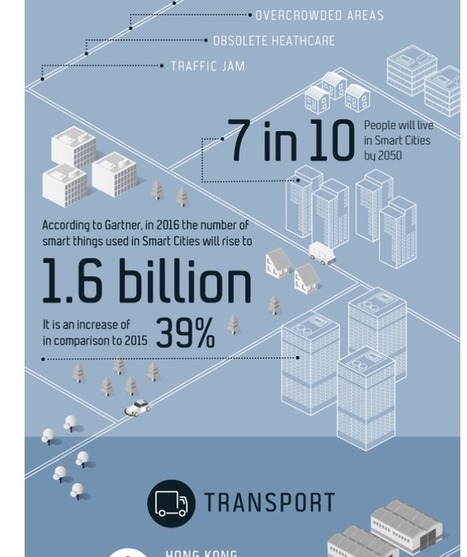
Cities are undoubtedly getting larger, especially in developing countries. This increase in size accelerates the consumption of resources and adapting will no longer suffice, they must develop sustainable economic strategies. To achieve this, a strong investment in human capital, social capital, urbanism and ICT infrastructure must be made. All over Europe start-ups are partnering up with governing bodies to innovate city infrastructure. Among others, this includes the smart use of data acquired by tech companies and by the government, improved mobility, energy efficiency and advanced connectivity, more commonly known as Internet of Things (IoT). Towards a smarter economy
A smarter economy is a crucial aspect to the Smart City movement. The notion has a broad meaning however Smart Cities Berkeley break it down into three different components; how Smart Cities technologies are changing urban commerce, the Smart City as an economic driver and the economics behind Smart Cities.
There is a lot of buzz at the moment about digitalising our economy, starting with payments. A clear illustration is the recent emergence of bitcoin or more broadly, mobile payments and e-wallets. Furthermore, there is a rise in the use of QR code technology or NFC (near field communication) for point of sale transactions. Indeed, mobile payments are at the heart of improving areas such as mass customisation retail, personalised tourism, enhanced mobility as well as peer to peer interactions. The end-game is to have a solution which digitalises the entire customer experience seamlessly. Learn more / En savoir plus / Mehr erfahren: http://www.scoop.it/t/21st-century-learning-and-teaching/?tag=Smart+Cities

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|
Two authors WHO have collaborated already since looong (see below links, please) on Global-Collaboration and learning together about ICT and everything around it, Cyber Security, Privacy , Digital CitiZenship are trying to show YOU, dear readers, THE possibilities on THE How-To to integrate Physical EDUcation within ICT and Social Media...
You will find as well links to software chosen by renowned Universities...

|
Scooped by
Gust MEES
|
Selon gizmag, nos chères têtes blondes s’attendent aujourd’hui à ce que les jouets offerts puissent se connecter à Internet et être couplés à des appareils intelligents, leur permettant ainsi d’accéder aux dernières tendances technologiques en date, parfois même avant leurs parents. Toutefois, chers parents, bien que nous ne puissions que vous recommander de réfléchir à deux fois avant d’acheter à vos enfants un jouet connecté, soyez vous aussi vigilants car, comme vous pourrez le lire ci-dessous, les risques de sécurité ne concernent pas uniquement les gadgets pour enfants.
L’Internet des objets (IdO) devient rapidement partie intégrante de notre réalité car un plus grand nombre de nos objets du quotidien renferment maintenant de l’électronique, des logiciels, des capteurs ou sont capables de se connecter au réseau, leur permettant ainsi de recueillir et d’échanger des données. Combien de ces objets, pensez-vous alors, peuvent se transformer en vrais chevaux de Troie ? La guerre de Troie prit fin quand les Grecs firent preuve de malice pour entrer dans la ville de Troie, cachant des soldats dans un énorme cheval de bois. Les Grecs firent semblant d’embarquer sur leurs navires et de prendre le large tandis que les Troyens, peu méfiants, s’emparaient du cheval en signe de victoire, le faisant entrer dans la ville. Plus tard cette nuit-là, les Grecs sortirent tant bien que mal dudit cheval de bois et ouvrirent les portes de la ville au reste de l’armée grecque afin que cette dernière pénètre dans la ville et la détruise. Quels attaquants peuvent potentiellement surgir de vos cadeaux de Noël ?
Learn more / En savoir plus / Mehr erfahren:
- http://www.scoop.it/t/21st-century-learning-and-teaching/?tag=wearables
- http://www.scoop.it/t/21st-century-learning-and-teaching/?tag=Internet+of+Things
- http://www.scoop.it/t/securite-pc-et-internet/?tag=Internet+of+things
- http://globaleducationandsocialmedia.wordpress.com/2014/01/21/why-is-it-a-must-to-have-basics-knowledge-of-cyber-security-in-a-connected-technology-world/

|
Scooped by
Gust MEES
|
Ihre tolle Smartwatch oder Spielerei könnte eine gewaltige Sicherheitslücke aufweisen ...
Früher lockte ein Weihnachtsbaum mit aufwändig verpackten Geschenken verführerisch Einbrecher an, von denen gerade in dieser Zeit des Jahres viele unterwegs waren. Heutzutage jedoch stecken unter dem bunten Geschenkpapier unter dem Baum technische Spielereien und mobile Geräte, die ein weitaus weniger offensichtliches und darüber hinaus kostspieligeres Risiko darstellen. Technische Spielereien, Spiele mit WLAN, Wearables, Tablets, Smartphones, Fitness-Tracker, Smartwatches, Handys und sogar größere Geräte wie Laptops zählen voraussichtlich zu den beliebtesten Präsenten dieses Jahr zu Weihnachten. Laut der britischen Spielzeughändlervereinigung sind in Großbritannien folgende 12 Spielzeuge die beliebtesten Weihnachtsgeschenke 2015; anfgeführt wird diese Liste von “Baby Toot-Toot Friends Busy Sounds Discovery House” des Herstellers Vtech. Sagt Ihnen Vtech etwas? Laut gizmag erwarten die Kinder von heute, dass sich ihre Spielzeuge mit dem Internet verbinden, mit smarten Geräten koppeln und oftmals noch vor ihren Eltern an den neuesten Trends in der Technologie teilhaben lassen. Allerdings sollten Eltern aus gutem Grunde sich wohl überlegen, bevor sie ihren Kindern technische Spielereien kaufen; denn wie Sie weiter unten sehen werden, weisen diese Risiken nicht nur Kinderspielzeuge auf.
Learn more / En savoir plus / Mehr erfahren:
- http://www.scoop.it/t/21st-century-learning-and-teaching/?tag=wearables
- http://www.scoop.it/t/21st-century-learning-and-teaching/?tag=Internet+of+Things
- http://www.scoop.it/t/securite-pc-et-internet/?tag=Internet+of+things
- http://globaleducationandsocialmedia.wordpress.com/2014/01/21/why-is-it-a-must-to-have-basics-knowledge-of-cyber-security-in-a-connected-technology-world/

|
Scooped by
Gust MEES
|
|

|
Scooped by
Gust MEES
|
There is no doubt that companies of all shapes and sizes are increasing their spend in internet-of-things (IoT) technology. In fact, IDC projects this to be a $1.4 trillion market by 2021. With the increased spend and demand by consumers for low-price and high-value IoT devices, makers of these connected technologies have put a premium on affordability. The race to the bottom on price has inadvertently created major risks for organizations and consumers, according to PwC’s “Uncovering the Potential of the Internet of Things” report.
The pressure is on, and we see many makers of connected devices that produce IoT products as inexpensively as possible skipping important steps such as the design of security and privacy protections. This is generating significant new risks that are not widely understood during a time when consumers are more concerned about price than privacy and security. Risks include physical, software, encryption and network attacks, all of which could have wide-ranging effects on our daily lives, from taking over a connected car to obtaining sensitive data from a connected home to accessing a private network via a wearable device. Also, there are societal concerns, including getting access to valuable intellectual property, sabotage to companies or governments and espionage. Consumer-focused companies need to ensure they are meeting their customers’ concerns. Simply put, the proper cybersecurity and privacy measures can aid businesses in seeing the full potential of IoT. Learn more / En savoir plus / Mehr erfahren: http://www.scoop.it/t/21st-century-learning-and-teaching/?&tag=IoT http://www.scoop.it/t/securite-pc-et-internet/?&tag=iot

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|
Did we learn nothing from Arthur C. Clarke's 1968 sci-fi epic, 2001: A Space Odyssey?
In the film, astronauts on a mission to Jupiter discover that the HAL 9000 artificial intelligence computer that controls and automates all functions on the spacecraft starts seriously glitching. The astronauts get worried, HAL gets paranoid -- yada, yada, yada -- HAL kills everyone on the ship.
Windows as a Service: What's it mean?
Microsoft's decision to unveil a subscription licensing model for Windows 10 for enterprises could be a
READ NOW
The moral of the story is that when lives depend on fully automated systems, it's a good idea to keep an eye on those systems anyway. (And if that's not the moral of the story, it should have been.)
How do you use something that's fully automatic, anyway? What is the responsibility of the "user"? Can we just hand over control to the bots?
Recent events in the news suggest that when it comes to using our automatic products and features, some people are doing it wrong. Learn more / En savoir plus / Mehr erfahren: http://www.scoop.it/t/21st-century-learning-and-teaching/?tag=Artificial+Intelligence http://www.scoop.it/t/securite-pc-et-internet?q=iot

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|
Pourquoi les entreprises s'intéressent-elles tant à la blockchain en ce moment ?
Primavera De Filippi : Cela dépend des entreprises. Pour les banques, les premières à s'emparer du sujet, il s'agit d'une technologie disruptive, qui risque de remettre en cause leur légitimité, mais qui a aussi énormément de potentiel pour améliorer leurs services. Certaines opérations bancaires, par exemple, ne peuvent pas être exécutées par un seul employé, notamment lorsqu'il s'agit d'importantes sommes d'argent. Il faut la signature de deux ou trois personnes différentes au sein de la banque. Avec la blockchain, on peut encoder toutes ces règles de procédure. Il n'y a plus besoin d'une autorité pour vérifier qu'elles sont appliquées : si les critères sont remplis, l'opération est automatiquement validée.
Des entreprises technologiques comme Samsung s'intéressent plutôt à la blockchain dans le cadre de l'Internet des objets (IoT). Elles veulent créer des dispositifs intelligents capables d'effectuer des échanges de valeur sur la blockchain, au lieu d'avoir simplement des appareils qui communiquent les uns avec les autres comme dans l'IoT traditionnel. Cela permet aussi de déléguer au dispositif la capacité de coordonner les échanges, sans avoir besoin de passer par un opérateur central qui va traiter toutes les informations et les renvoyer. Car lorsque nous serons dans un système où des trillions d'appareils communiqueront les uns avec les autres, aucun serveur central ne sera capable de gérer tous ces échanges.
Learn more / En savoir plus / Mehr erfahren: http://www.scoop.it/t/21st-century-learning-and-teaching/?tag=blockchain

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|
According to gizmag, today’s kids expect their toys to connect to the internet, pair with smart devices, and let them join in the latest tech trends, often before their parents. However, while there are good reasons parents should think twice before buying tech toys for their kids, as you will read below, security risks aren’t just confined to gadgets for children.
As the concept of the Internet of Things (IoT) rapidly becomes reality as more and more objects are embedded with electronics, software, sensors and network connectivity that enables them to collect and exchange data, how many of your Christmas gifts could be the equivalent of the Trojan Horse? It was a decisive end to the Trojan War when the Greeks used subterfuge to enter the city of Troy, hiding some of their army inside a huge wooden horse. After pretending to sail away, the unsuspecting Trojans pulled the horse into their city as a victory trophy. Later that night the Greek force crept out of the horse and opened the city gates for the rest of the Greek army to enter and destroy the city. What attackers could be potentially unleashed in your Christmas gifts?
Learn more:
http://www.scoop.it/t/21st-century-learning-and-teaching/?tag=Internet+of+Things
https://globaleducationandsocialmedia.wordpress.com/2014/01/21/why-is-it-a-must-to-have-basics-knowledge-of-cyber-security-in-a-connected-technology-world/

|
Scooped by
Gust MEES
|
|



 Your new post is loading...
Your new post is loading...



























With blockchain implemented, a device cannot access a network unless it is verified through the entire ledger. In this scenario attacks like Mirai become significantly more difficult, if not impossible, because a hacker would need to modify the entire ledger, and not just the credentials of any one device.
Ericcson Research demonstrated a proof-of-concept of this idea at the 2017 Mobile World Congress in Barcelona this past March. The researchers set up a small WiFi network that used blockchain authentication instead of a typical username/password setup.
Learn more / En savoir plus / Mehr erfahren:
https://www.scoop.it/t/21st-century-learning-and-teaching/?&tag=blockchain